
[ad_1]
The CEO of widespread encrypted password supervisor LastPass has mentioned that the hacking episode final month didn’t contain any entry to prospects’ information or encrypted password vaults.
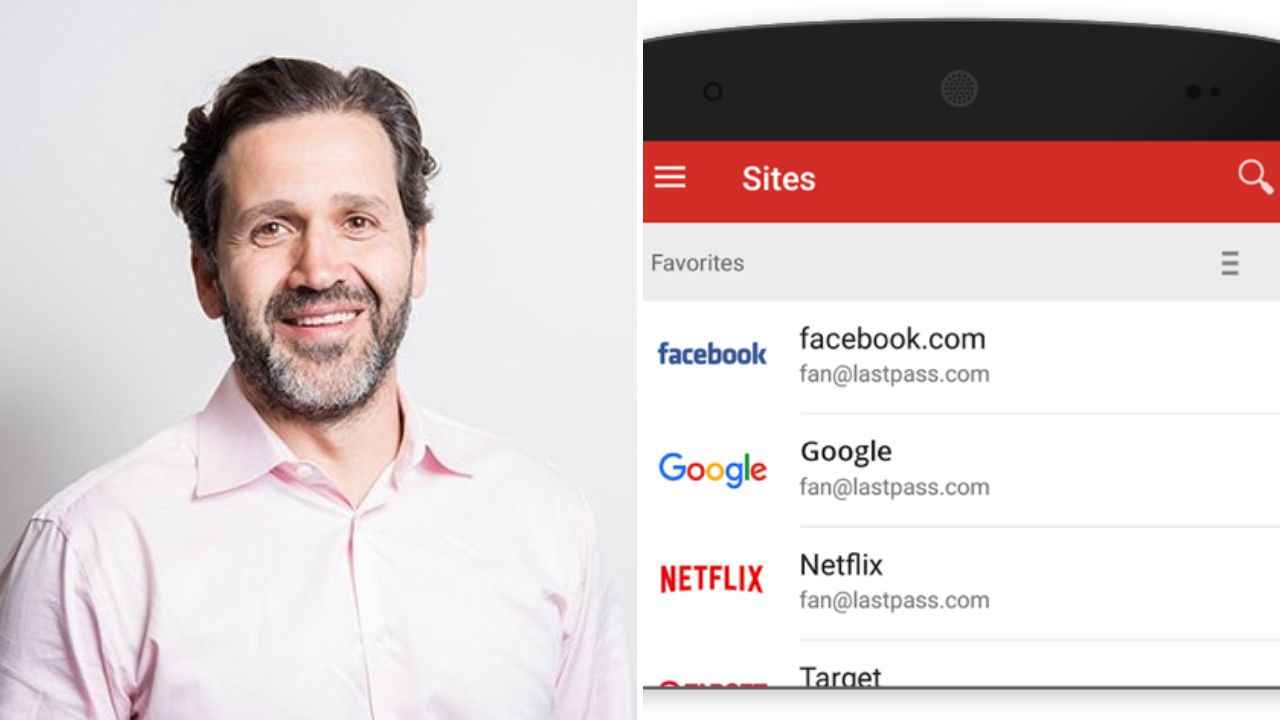
In a contemporary assertion, Karim Toubba, CEO of LastPass admitted that the safety breach in August had inside entry to the corporate’s techniques for 4 days till they have been detected and evicted.
“Our investigation revealed that the risk actor’s exercise was restricted to a four-day interval in August 2022. During this timeframe, the LastPass safety staff detected the risk actor’s exercise after which contained the incident,” Toubba mentioned.
The investigation discovered that the risk actor gained entry to the platform’s growth atmosphere utilizing a developer’s compromised endpoint.
The risk actor utilised their persistent entry to impersonate the developer as soon as the developer had efficiently authenticated utilizing multi-factor authentication.
“Although the risk actor was in a position to entry the Development atmosphere, our system design and controls prevented the risk actor from accessing any buyer information or encrypted password vaults,” mentioned the CEO.
LastPass is a freemium password supervisor that shops encrypted passwords on-line.
The CEO mentioned that LastPass doesn’t have any entry to the grasp passwords of its prospects’ vaults.
“Without the grasp password, it’s not potential for anybody apart from the proprietor of a vault to decrypt vault information as a part of our Zero Knowledge safety mannequin,” he talked about.
The firm mentioned it has deployed enhanced safety controls, together with further endpoint safety controls and monitoring after the incident.
(Except for the headline and canopy picture, the remainder of this IANS article is un-edited)
For extra know-how information, product critiques, sci-tech options and updates, maintain studying Digit.in
[ad_2]